The Teem app does so much more than conference room digital signage — it can change the way your staff uses your office space.
Limit the number of employees in conference rooms, desk areas and common spaces. Teem displays the maximum number of occupants for each designated space, making it easy for employees to choose where to hold their next conference call or settle in for the day.
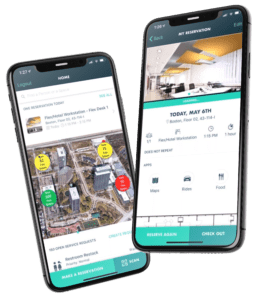
What if the room someone wants to reserve is already occupied? Employees can use meeting room displays from Teem to find out which other rooms are available, then book an available space anywhere – right from the display they’re currently viewing or from their mobile device (iOS and Android) with the Teem app.
Teem Helps Your Institution Work Better Together, Creating a More Productive Environment.

Manager Meeting Tools
That connects your people with the right resources for meetings when and where they need them.
- – The eye-catching conference room displays showroom availability at a glance and accepts ad hoc bookings right from the display.
- – Mobile booking allows faculty to search for the best meeting room and resources for their needs, then book the meeting right from their phone
Activity Driven Insights
That dig deep into your facilities’ meeting and space use behaviors, giving you answers to questions about how your people, places and technology interact, such as:
- – Find out which rooms are under or over-utilized.
- – Discover how often meetings are canceled
- – See if you need to expand, consolidate or repurpose current space or plan new spaces
- – Calculate how much meetings are costing your institution
Teem is the Secret Weapon for a Better Institution
- – Runs on affordable, readily available hardware (iPads® / Android® )
- – Syncs with popular calendar systems such as Microsoft Exchange, Office 365, Outlook and Google
- – It’s easy to implement and scale-up across buildings, floors, and campuses
- – Strict security policies include incident response management procedures, user access control, SSL data transport, data encryption and routine pen tests